What is DNSSEC and Why is it Important for Cybersecurity?
Domain Name System Security Extensions or DNSSEC is a set of DNS extensions that provide cryptographic data validation. It was developed by the IETF or Internet Engineering Task Force to authenticate data exchanges between computers so that hackers cannot intercept, modify, or even read the data. It improves over other security measures because it prevents data from being forged. It can be used to ward off cyber threats by providing security to web browsing and email traffic, and it will also prevent DNS cache poisoning by hackers.
This article will learn what DNSSEC is and why it is important in cybersecurity.
How does DNSSEC work?
The Domain Name System Security Extensions (DNSSEC) goes way beyond basic DNS resolution. It is designed to protect against malicious tampering and spoof DNS data by using cryptographic authentication, integrity, and anti-reflection measures.
Authentication is basically the procedure of confirming that the information received by a party is authentic and accurate. This process would not be complete without data integrity, which ensures that any changes in data are detectable by comparing it to what was originally sent.
There are two parties involved in DNSSEC: the owner of the zone (the zone administrator) and all DNSSEC-enabled DNS servers in the domain zone hierarchy below them (resolvers). Resolvers implement authentication, while zone administrators implement data integrity.
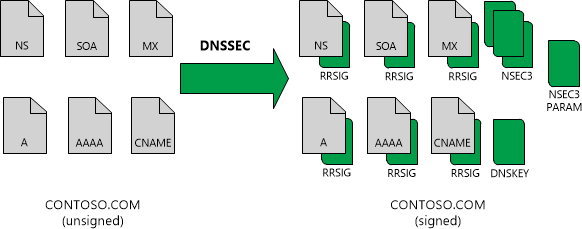
DNSSEC is an internet security mechanism that adds validation to a zone, and it does not change the basic DNS mechanism of a query and response. With DNSSEC, an authoritative DNS server can secure a DNS zone. To validate DNS responses, it uses digital signatures. These DNSKEY RRs contain the digital signature of the key used to sign them.
This diagram shows DNS resource records in the zone contoso.com before and after zone signing.
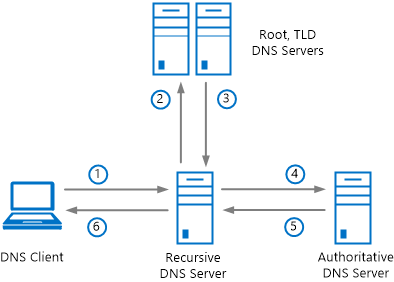
A DNS client computer queries a recursive (caching) DNS server, which in turn queries authoritative DNS servers before returning a response. This example assumes that DNS data is not yet cached on the client or server. A DNSSEC-signed zone is an important component of a secure internet. The following figure shows the recursive DNS query process.
DNSSEC is a protocol that provides a digital signature for a domain name to enhance the identification and validation processes. It also helps with the integrity and confidentiality of data.
The primary benefits of DNSSEC are:
– Protects user privacy
– Prevents DNS hijacking
– Protection from man-in-the-middle attacks
– Provides authentication and authorization of domain information
– Prevents cache poisoning
DNSSEC ensures that all data is encrypted and cannot be read by an eavesdropper. These features make DNSSEC a very useful security protocol for protecting against cyberattacks.
Why is DNSSEC important, and how does it affect your cybersecurity?
DNSSEC is important because it provides a security protocol that protects DNS data by cryptographically signing it. This protects the integrity and authenticity of the data, ensuring that those who are not authorized to change it cannot do so.
DNSSEC can improve your cybersecurity by making cyberattacks more difficult or completely preventing them from affecting the victim’s system. It also protects against tampering with information and “spoofing” attacks where hackers pretend to be a legitimate site for malicious purposes.
Without DNSSEC, DNS data could be modified or forged by a third party without anyone knowing about it because DNS is a distributed database, meaning it is spread over many different servers around the world.
Conclusion
Cyberattacks are increasing in number and complexity. Hackers are becoming more sophisticated, and they have to be dealt with promptly because if not, the costs can be huge. DNSSEC security will only become more important as time goes on unless there are more advanced solutions created in the future to solve this problem.
Tags: cloudflare, dns, dnssec, dnssec advantages, dnssec godaddy, dnssec-enable, dnssec-validation, domain, domain name system dns, hosting
Recent Comments
No comments to show.Archives
Categories